i3 products include software that has been designed to allow organizations to better govern and manage the information that flows through their organization. These software products allow a company to improve the value they are able to derive based on the data they create as well as improving the value of the data obtained from partnered organizations.
i3 Software

i3 Core Software. The i3 core software facilitates the management of information that flows in real-time across their data network. This includes the information that flows between applications and the information that flows from IoT devices to data lakes and applications. The original i3 Software was developed by the I3 Consortium, and released as opensource software to support research, developers, and other users. i3 Systems has taken this core concept and put it on steroids to create a robust and greatly enhanced version of this software which includes features needed to support demanding commercial deployments of these systems.
Edge Processing

i3 Edge Processing. As a compliment to the i3 core software, i3 has developed an edge processing system that allows key software functionality to be moved to the edge of the network where data is generated or consumed. By moving key software components from the cloud to the edge of the network, overall performance can be improved, however, perhaps more importantly information security and privacy can be improved. By performing certain functions at the edge of the network security features can be applied before the data is presented to the communications network, sensitive PII information can be removed or anonymized, and messages can be enhanced to better characterize information provenance.
Governance-Audit Features

Governance-Audit Features. Legislative efforts that are focused on security and privacy issues often require periodic data audits to ensure an organization is cognizant of the data it has and how it is being used. Industry best practices already suggest regular data audits be adopted as a standard operational practice. These information audits should be conducted regularly within the organization and should also be conducted with partners and suppliers to validate that established data-sharing agreements do not result in activities that could tarnish the organization’s reputation and open the door to legal liabilities. The i3 software provides tools that support organizations in their efforts to ensure organizational compliance with corporate policies and industry best practices for privacy and security.
API Tools/Features

API Tools/Features. The i3 software includes software tools that aid organizational efforts to deploy information networks as a part of their infrastructure. Dat streams entering or exiting the i3 information network pass through an adaption layer where data wrapper processes can enhance or reformat the data stream to match organizational requirements. Information flows from different sources with differing formats can be easily restructured to follow the organization’s internal information standards. Information flows from multiple sources can also be combined to create embellished information flows that enrich the value of the messages flowing through the system.
Federated Operations
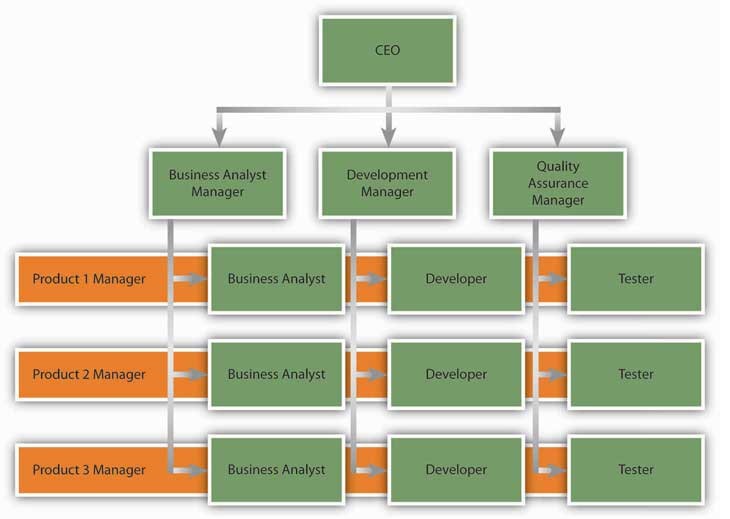
Federated Operations. A critical issue associated with information networks is that it has to be designed to function in federated environments. If an information network is designed around and intended for use by IT professionals, these highly valuable resources quickly become an operational bottleneck that impedes organizational operations. i3 Systems designed their software so the IT team is the facilitator of the information network but the information ownership and the day-to-day operational decisions are put in the hands of the data owners. This design allows the i3 software to be fit into an existing organizational structure rather than creating an information network that requires a restructuring of operational functions in order to succeed.